 I opened my own business in the early 1990’s that specialized in computers and networking. After relocation to Nashville in 1999, I became the IT Director of a local petroleum company designing a enterprise VOIP system. My education and training includes a BS in Business and Org. Mgmt. in 2006, MCSE in 2009 and MBA in 2011. I am currently the Director of IT for a International Truck dealership in Tennessee.
I opened my own business in the early 1990’s that specialized in computers and networking. After relocation to Nashville in 1999, I became the IT Director of a local petroleum company designing a enterprise VOIP system. My education and training includes a BS in Business and Org. Mgmt. in 2006, MCSE in 2009 and MBA in 2011. I am currently the Director of IT for a International Truck dealership in Tennessee.
It does not seem to matter where you are at while on the road, getting that high speed connection is just always out of reach – well, out of reach of your current PC, that is. You would think that having setup hundreds of Wi-Fi for both business and home users that this would not be such an issue for me, but it is if I am not prepared. After finishing a recent redesign of a Wi-Fi system for a campground I realized that the issues that most users were having had nothing to do with the availability of the signal but had more to do with how they were trying to connect to the signal provided.
 As avid Airstreamers we often sit inside on a wet cold day wanting to get online for such things as weather reports and e-mail without realizing we are sitting in an almost perfect isolation chamber for Wi-Fi signals. Even the use of cellular digital packet data card (CDPD), also known as a cellular modem or a Cell USB dongle, which is one of those things the cellular company sells you to let your computer work on their service, is often useless at your location due to no cellular antenna nearby. From inside the campground, Wi-Fi and CDPD were not able to be seen by the internal cards on my laptop as long as I was sitting inside the trailer. Getting service is not just about what you use to connect but also what is available where you are and what is needed to get a connection at that location. As CDPD is dependent on cellular tower location and we as consumers have little say as to where they should be put, the rest of this article will concentrate on Wi-Fi and its use as an internet connection.
As avid Airstreamers we often sit inside on a wet cold day wanting to get online for such things as weather reports and e-mail without realizing we are sitting in an almost perfect isolation chamber for Wi-Fi signals. Even the use of cellular digital packet data card (CDPD), also known as a cellular modem or a Cell USB dongle, which is one of those things the cellular company sells you to let your computer work on their service, is often useless at your location due to no cellular antenna nearby. From inside the campground, Wi-Fi and CDPD were not able to be seen by the internal cards on my laptop as long as I was sitting inside the trailer. Getting service is not just about what you use to connect but also what is available where you are and what is needed to get a connection at that location. As CDPD is dependent on cellular tower location and we as consumers have little say as to where they should be put, the rest of this article will concentrate on Wi-Fi and its use as an internet connection.
The first task is to determine your level of Wi-Fi use. Will you be using Wi-Fi a lot inside your RV or just on occasion? If your answer is just on occasion then your solution may be as simple as sitting close to an open window and using plastic screening in the window and not aluminum screening material. If you answer a lot, then you need to consider a solution that can be easily setup but removed for travel. This solution is the one we will be considering in greater detail a little later on. While some of these suggestions have been shown to me by other computer users, some of them are NOT supported by the manufacturers of the devices and are not recommended by me due to inherent dangers to users or equipment.
The first solution was shown to me by a full timer who worked mostly outside his trailer, but needed an option for those rainy days. The solution was to use a six foot USB cable extension and to purchase a USB Wi-Fi adapter; this could have been just as easily one of those CDPD adapters. He ran the six foot cable from his table next to the RV refrigerator through the wall and out through the refrigerator vent where he had attached the stand that came with the USB Wi-Fi adapter to the vent at an angle using silicone to help keep water out. At this point he would use compressed air to get any water out of the connector, then plug the Wi-Fi adapter into the cable and cover it with a freezer bag and zip tie, then go plug the other end into the laptop. Unfortunately there are just a few issues with this. First, the USB port on most computers is powered as part of the laptop’s main board voltage and power source of 5 volts, so if you short it out, you short the main board on PC. The second issue is that a USB connection is not meant for OUTDOOR USE! When I mentioned this to him, he assured me that he had been using this setup for about two years, so I wished him continued luck. If you wanted to run a similar setup for an inside solution which would allow you to move the USB adapter closer to a window, then I would agree with this solution as long as it there is no risk of getting the adapter or cable wet.

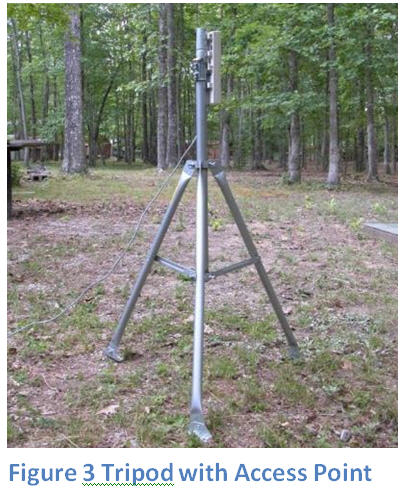 My suggestion for mounting the units would be something as simple as using a zip tie and putting it on your awning pole or using a portable tripod such as the ones made for satellite dishes, which allows you to move it around for the best positioning. You could mount both on the same tripod (see Figure 3) given enough vertical pole space. The second suggestion would be to use shielded twisted pair instead of unshielded and use a grounding strap to ground the shielding on the cable to an earth ground to prevent either a short in your electrical system or other such issues doing damage to the equipment.
My suggestion for mounting the units would be something as simple as using a zip tie and putting it on your awning pole or using a portable tripod such as the ones made for satellite dishes, which allows you to move it around for the best positioning. You could mount both on the same tripod (see Figure 3) given enough vertical pole space. The second suggestion would be to use shielded twisted pair instead of unshielded and use a grounding strap to ground the shielding on the cable to an earth ground to prevent either a short in your electrical system or other such issues doing damage to the equipment.
 The next question I often get asked about is the usage of a repeater. It has been my experience that the use of a repeater has a several drawbacks such as their ability to create a broadcast storm, which is caused by sending the same packet of information through multiple wireless devices and will cause wireless to fail. The second rule for the use of a repeater is that it should only be one “hop” from the AP being used; that is, you should not have a repeater able to communicate to a second repeater as this increases the potential for a broadcast storm. If you are in a limited area and want to provide connectivity for a group and extend the range of the AP, a repeater is a simple solution and many of the advanced APs have a multi-mode operation where they can be setup as an AP, CAP, or repeater. These provide the best versatility based on the situation you find yourself. The most notable of these is the CDPD repeaters being offered that allow a group to share a single CDPD connection. These are often limited to five devices (a device is any item that has an IP address) and have a limited range of less than 15 feet from the sending device. Also keep in mind these do require the use of a cellular service that is in range.
The next question I often get asked about is the usage of a repeater. It has been my experience that the use of a repeater has a several drawbacks such as their ability to create a broadcast storm, which is caused by sending the same packet of information through multiple wireless devices and will cause wireless to fail. The second rule for the use of a repeater is that it should only be one “hop” from the AP being used; that is, you should not have a repeater able to communicate to a second repeater as this increases the potential for a broadcast storm. If you are in a limited area and want to provide connectivity for a group and extend the range of the AP, a repeater is a simple solution and many of the advanced APs have a multi-mode operation where they can be setup as an AP, CAP, or repeater. These provide the best versatility based on the situation you find yourself. The most notable of these is the CDPD repeaters being offered that allow a group to share a single CDPD connection. These are often limited to five devices (a device is any item that has an IP address) and have a limited range of less than 15 feet from the sending device. Also keep in mind these do require the use of a cellular service that is in range.

The final note
about wireless is about security. When you link to a wireless, your information
can be seen by others on the wireless if it is not secure. When you connect to
a wireless you should use one of the common security encryption protocols such
as WPA or the less secure WEP. While the use of encryption does NOT guarantee
true security unless you control the access point and do not share the
encryption key, which is not likely while Airstreaming, you are going to have
to put some trust in the network owner. This is considered the first layer of
security. The second layer should be to never use websites for personal
transactions such as banking or other financial transactions, online shopping,
or even e-mail if the site does not employ a two-part authentication process and
some type of encryption.